Office 365 Email Administrative Setup: Difference between revisions
Jspenceratty (talk | contribs) |
Jspenceratty (talk | contribs) |
||
| Line 94: | Line 94: | ||
> | > | ||
|- | |- | ||
| | | token Uri || <copy value the App registration, click on Endpoints and enter the value from "OAuth 2.0 token endpoing (v2)". That should look like this: | ||
<nowiki>https://login.microsoftonline.com/<your directory tenant id>/oauth2/v2.0/token</nowiki> | |||
|} | |} | ||
Close this form to save the entries. | |||
Revision as of 19:26, 9 December 2022
Office 365 Azure Active Directory Setup
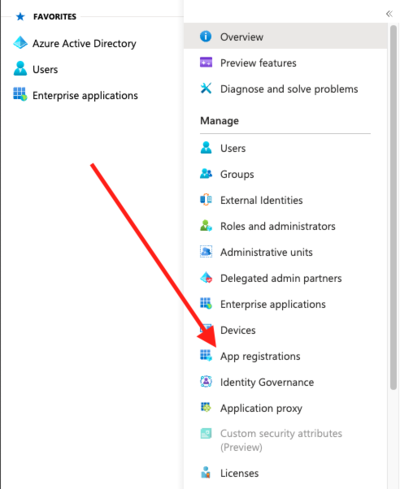
In the Azure Active Directory menu, click on "App registrations"
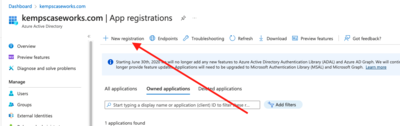
At the top of the "App registrations" page, click on the "+ New Registration" link
In the "Register an application" page:
- Enter a "Name" for the application, for example, "Prime 16 Email Application".
- Leave the "Supported account types" selection of "Accounts in this organizational directory only".
- In "Redirect URI", choose "Public client/native (mobile & desktop)" and enter "http://localhost:3017" in the next box.
- Click the "Register" button
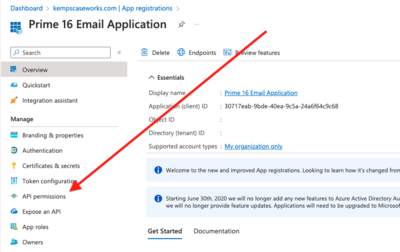
This should return you to the new app registration. Your chosen Name for the application should appear at the top of the form. Now click on the "API permissions" link
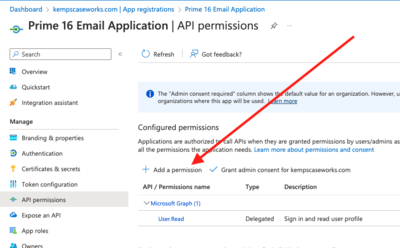
In the "API permissions" page, click on the "+ Add a permission" link
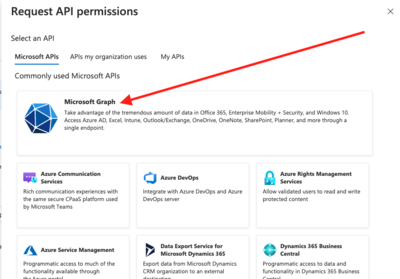
In the "Request API permissions" box, select "Microsoft Graph"
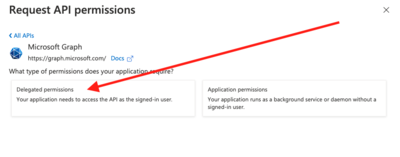
When asked "What type of permissions does your application require?", choose "Delegated permissions"
From the resulting list below that, check the box next to the following options;
OpenId permissions:
- offline_access
- openid
- profile
IMAP
- IMAP.AccessAsUser.All
MailboxSettings
- MailboxSettings.Read
- Mail.Read
- Mail.Read.Shared
- Mail.ReadWrite
- Mail.ReadWrite.Shared
- Mail.Send
- Mail.Send.Shared
POP
- POP.AccessAsUser.All
SMTP
- SMTP.Send
User
- User.Read
Click "Add permissions" at the bottom of the "Request API permissions" box.
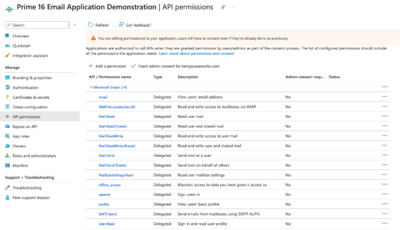
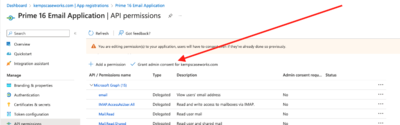
The resulting page should look like this:
Click "+ Add a permission" link in the "API permissions" page.
This time, select "APIs my organization uses" at the top. In the search box, enter "Office 365 Exchange Online". Choose the resulting entry, then choose "Delegated permissions". Then, in "EWS" select the "EWS.AccessAsUser.All" entry. Choose "Add permissions" at the bottom.
Click the "Grant admin consent for kempscaseworks.com" at the top of the "API permissions page". And choose yes. This will keep users from seeing the "Do you grant consent to this application page" when they attempt to use the Email system
Prime 16 Setup
Within Prime 16, got to the "Admin" top line menu and choose "Custom Admin" and choose "O365 Setup". Enter the values as follow:
| Item | Entry |
|---|---|
| OnlyOneRowAllowed | True |
| Redirect URI | http://localhost:3017 |
| the Client ID | <copy value for Application (client) ID from the App registration you created above as shown File:Screenshot 2022-12-09 at 1.17.45 PM.pnghere> |
| client Secret | <Enter a random string, for example: jo2i3jutr98uyxcvoijkn2> |
| scope | https://outlook.office.com/IMAP.AccessAsUser.All%20offline_access%20email%20openid |
| auth Uri | <copy value the App registration, click on Endpoints and enter the value from "OAuth 2.0 authorization endpoing (v2)". That should look like this:
https://login.microsoftonline.com/<your directory tenant id>/oauth2/v2.0/authorize > |
| token Uri | <copy value the App registration, click on Endpoints and enter the value from "OAuth 2.0 token endpoing (v2)". That should look like this:
https://login.microsoftonline.com/<your directory tenant id>/oauth2/v2.0/token |
Close this form to save the entries.